Identity & Access Governance (IAG/IGA) capabilities
Policy-driven requests, risk-aware approvals, SoD controls, and audit evidence governed with JIT/time-bound access.
Learn moreWelford IAG helps enterprises control access across systems, roles, and entitlements with policy-driven workflows, just-in-time (JIT) / time-bound access, and audit-ready evidence. Reduce standing access, standardise approvals, and prove compliance with end-to-end traceability.

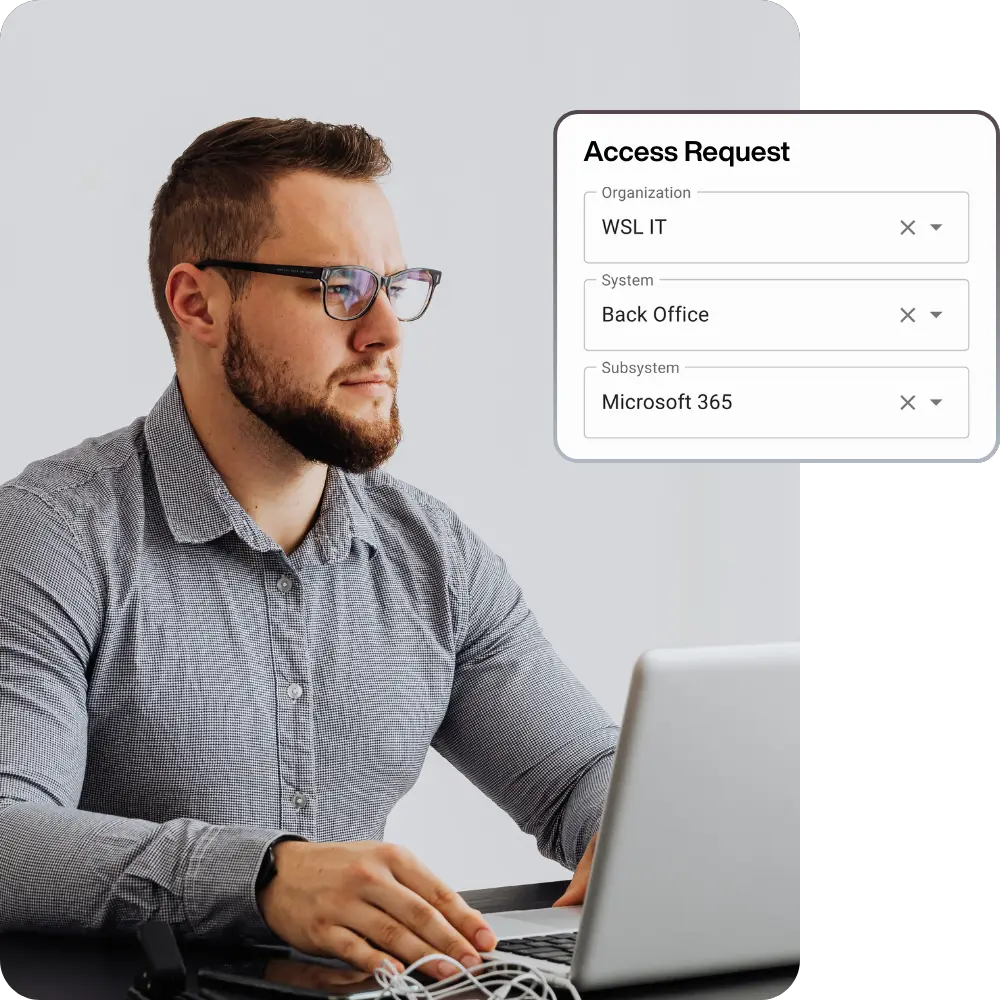
Welford IAG enables users to request access and routes approvals based on policy, ownership, and risk level.
Welford IAG governs all access using just-in-time/time-bound approvals to reduce standing access and enforce least privilege.


Welford IAG governs lifecycle access changes with controlled approvals and traceable evidence.
Welford IAG maintains an entitlement catalogue with ownership to support accountability and consistent approvals.


Welford IAG provides end-to-end traceability across requests, approvals, fulfilment, and expiry/revocation.
Welford IAG provides visibility into current and historical access for authorised stakeholders and auditors.

Welford IAG strengthens enterprise identity security with advanced capabilities designed for high-risk access and complex environments.
Policy-driven requests, risk-aware approvals, SoD controls, and audit evidence governed with JIT/time-bound access.
Learn moreVault, reveal, rotate plus API-only "no-human reveal" secrets and auditable privileged credential lifecycle events.
Learn morePassword-less, time-bound Linux privileged access with approval linkage, automatic expiry/revoke, and audit evidence.
Learn moreEncrypted password storage with controlled retrieval and audit logging reducing reliance on browser/local password stores.
Learn moreAutomate access lifecycles where integrated; orchestrate tickets where not with governance evidence preserved end-to-end.
Learn moreWelford IAG helps enterprises control access across systems, roles, and entitlements with policy-driven workflows, just-in-time (JIT) / time-bound access, and audit-ready evidence. Reduce standing access, standardise approvals, and prove compliance with end-to-end traceability.